Connect Your Smartphone via VPN with Two Factor Authentication
March 04, 2013 •
Most days when I am on the road or outside the office I have a real need to access our internal network to review documents, specs or access the internal portal. In order to have secure anytime, anywhere access to our corporate resources and applications our engineering team has deployed a VPN server for remote access. While at a client site or in a coffee shop my smartphone, which is already online and ready to go, is ideal for quick VPN access. Being in the online authentication platform business, we already access our VPN with two-factor authentication using LoginTC on remote desktops and laptops. Username/password only on the smartphone was naturally not an option. Below is how to enable two-factor authentication on your mobile device for secure remote access. Before that, let’s briefly talk on what needs to be done on the corporate network side.
Server side setup
In order to use virtual private networking, you need a VPN server configured on the network to which you want to connect. We deployed OpenVPN, which is quite a robust VPN solution that can be configured to use RADIUS authentication. Once our engineers installed the OpenVPN VM server, they proceeded to install and configure our LoginTC RADIUS Connector, a free virtual appliance that integrates with RADIUS-based devices such as VPNs to use LoginTC. If you happen to have commercial VPNs such as Barracuda, Cisco ASA or Juniper SA series it is also quite easy to integrate them with the LoginTC RADIUS Connector. The instructions provided to install and configure the connector are straightforward and you can have your VPN protected in under an hour.
Preparing My Smartphone for VPN
In mid-January 2013 OpenVPN released iOS OpenVPN Connect, a VPN client app for iOS. Since I already had a credential to access our office VPN in my LoginTC app, it was as easy as to download the OpenVPN app on my iPhone, and get the OpenVPN profile from our engineers to provision remote access via our corporate VPN on my smartphone. OpenVPN also has an Android OpenVPN Connect client app you can use for the same purpose.
Nowadays, all smartphones have built-in VPN clients, with well explained instructions on how to setup your iPhone / iPad, Android and BlackBerry devices. Typically these built-in clients already provide VPN remote access to their users, but they lack the security of two-factor authentication. If you are using a built-in VPN client with your smartphone, LoginTC can add an additional layer of security.
Accessing the VPN
To access my office network via VPN, I simply launch the OpenVPN app and select our corporate VPN profile. You can also initiate the same sequence if you are using the built-in VPN client in your smartphone, or one of the multiple apps distributed by VPN vendors: CISCO AnyConnect app, Junos Pulse app from Juniper, Mobile VPN app from Check Point, etc.
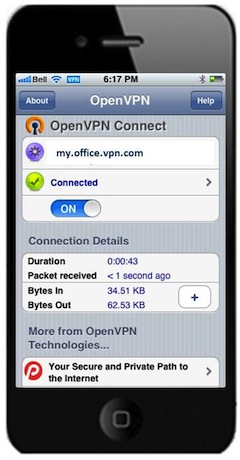
The OpenVPN app has the profile my.office.vpn.com already loaded. It contains all the configuration and corresponding certificates to reach the VPN server in the office. Loading the profile was as simple as receiving an internal email in my smartphone with the profile file and being prompted to load it with the OpenVPN app.
We decided to continue using the 1st factor authentication username/password to initiate the session. We use an LDAP directory as the authoritative source. The role of the LoginTC RADIUS Connector at this stage is crucial. It traps the request for 1st factor authentication and orchestrates the two-factor authentication sequence; granting access only once both factors are satisfied.
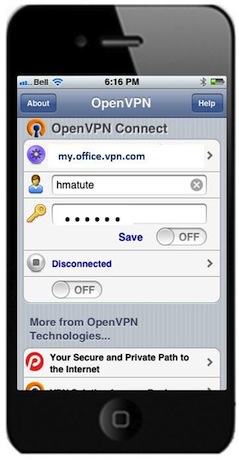 OpenVPN App
OpenVPN App
 First factor
First factor
LoginTC two-factor authentication
Once the LoginTC RADIUS Connector gets a successful confirmation of the username/password, it initiates a wireless notification to my smartphone. Opening the notification launches the LoginTC app where I confirm the access and unlock the token with a 4-digit PIN. The LoginTC administrator can configure the strength of unlocking the token with either a 4-digit PIN or a passcode.

2nd Factor
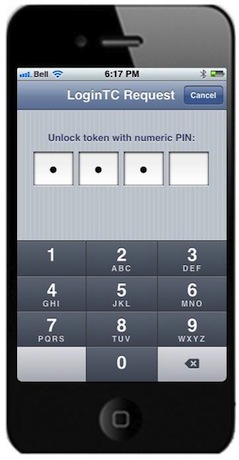
Verification
Once the correct 4-digit PIN is entered, the configured LoginTC RADIUS Connector confirms the successful unlocking of the VPN token credential and access is granted!
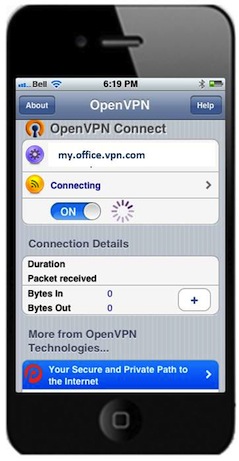
Connected to VPN
Opening OpenVPN Connect confirms the smartphone is connected to our office VPN. A highlighted VPN symbol in the Status Bar is also shown.
At this point the mobile browser can point to an internal URL or to an enterprise app that only works behind the VPN.
Connected to office VPN!
Summary
Connecting to the office VPN with my smartphone has saved me quite a bit of time in retrieving documents or researching the latest reports.
By enabling your smartphone or tablet with two-factor authentication, you also enhance the security and compliance of your organization. Two-factor authentication is required to comply with PCI DSS Requirement 8.3 (the Payment Card Industry Data Security Standards) to access Cardholder Data Environment (CDE) remotely. According to the document, e-commerce merchants hosting cardholder information must “incorporate two-factor authentication for remote access (network-level access originating from outside the network) to the network by employees, administrators, and third parties”.
In the health industry two-factor authentication is also recommended in order to meet HIPAA compliance, adding an extra layer of security to prevent unauthorized access to health records.
For those organizations that have mandatory compliances for remote access or security-conscious companies that want to protect intellectual property and internal information, two-factor authentication with your mobile access sessions can offer significantly more security with minimal effort and cost.