How to set up your VPN with LoginTC 2FA
March 05, 2015 •
Introduction
According to Forrester Research, at least 82% of companies now have virtual private networks (VPNs) in place, up sharply from 55% in 2003. Whether you’re a small-medium sized business (SMB), or a global enterprise, chances are you’re in the same boat.
But, unless you’re using two-factor authentication (2FA) to protect your network, the corporate resources that run behind your VPN are not secure. And unless you’re using LoginTC, it’s possible you’re needlessly sacrificing user experience and economic value for security — which does not have to be the case. With LoginTC you get high security at low cost. Have your 2FA-flavoured cake and eat it too (with icing made of ingredients like scalability, simplicity, cloud computing, contextual information, and push notifications that work worldwide).
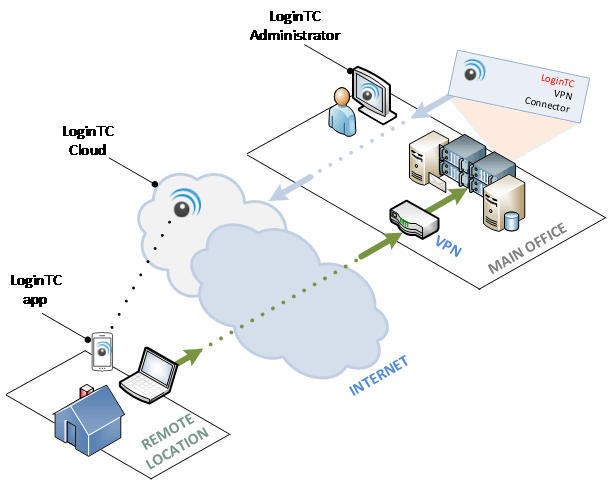
LoginTC leverages and supports YOUR infrastructure: a RADIUS-speaking VPN, and mobile devices or desktops. We’ve created detailed, custom docs guiding deployment for Cisco ASA, OpenVPN, OpenVPN Access Server, WatchGuard and other systems. Whatever your system and whatever device your end-users choose to enable (Apple, Android, or desktop via Google Chrome), LoginTC is simple to set up.
How to enable LoginTC 2-factor on your VPN (in 10 easy steps)!
Step 1: Check your prerequisites
- Have you signed up for a LoginTC Admin account?
- Do you have computer virtualization software, such as VMWare ESXi or VirtualBox?
- Does your Virtual Machine meet these requirements: 1024 MiB RAM, 8 GiB disk size?
Step 2: Create a Domain
- In LoginTC Admin, click Domains. Then Create Domain. (The domain represents the VPN you want to protect with LoginTC.)
Step 3: Install
- Download the latest LoginTC RADIUS Connector and then unzip the file.
- Import the Open Virtualization Format (OVF) file into your computer virtualization software and start the virtual appliance.
Step 4: Navigate the console dashboard
- Once you set the LoginTC user password (default: logintcradius), decide whether you want to configure the appliance network by DHCP (default) or manually (Network Configuration / DNS Configuration). To access the extremely user-friendly web-based interface, select Web Server then Start.
Step 5: Navigate to the web interface
- Just type the URL presented in the information box into your web browser!
- Thanks to this new GUI, 2FA configuration takes you minutes as opposed to hours!
Step 6: Configure
- The GUI will walk you through the next steps, step-by-step in a very straightforward manner. It will ask you to configure your LoginTC settings (which LoginTC organization and domain to use), the optional first factor authentication that will be used in conjunction with LoginTC, your RADIUS client (VPN) and offer an encryption option. Just fill in the forms.
Step 7: Test
- Although you will have already passed through mandatory testing at every stage of the process in order to highlight any possible errors that occurred along the way, you will now conduct a final test of your configuration by creating a test user in LoginTC Admin.
- Issue Token to your test user and enter the Activation Code that appears beside the username into the user’s LoginTC mobile or chrome app to create a credential. Lock with a PIN or passcode.
- Return to the GUI and Test Configuration.
- The user should receive a simulated authentication request!
Step 8: Configure your RADIUS Client
- Now that LoginTC is set up, set your RADIUS device to use the LoginTC RADIUS Connector as its authentication source, and set the RADIUS timeout to 60 seconds to allow enough time for LoginTC authentication responses.
Step 9: Manage your users
- Enroll your users and provision their tokens from LoginTC Admin. There are several options for this so choose the one that best suits your needs.
Step 10: Breathe easier because your network is protected by LoginTC!
*NOTE: All the above information is available in greater detail WITH GRAPHIC/IMAGE-BASED INSTRUCTIONS on our docs page.
Conclusion
Competitors make you putter around with proxy service installation, configuration files, or even extra inventory in the form of hard tokens or other hardware. LoginTC believes in high security without the hassle. Not only is LoginTC a top-of-the-line cybersecurity solution, it’s also clearly one of the simplest-to-use 2factor authentication systems around — from admin installation/configuration to end-user experience. Get started now!
If you’re enjoying learning about how to set up LoginTC and don’t want the fun to end, here are some bonus steps you can take:
- Contact us for help, support or feedback
- Recommend us to a friend or colleague
- Rate us in the app store (and/or ask end-users to do the same)
- Follow us on Twitter or LinkedIn
- Check on the service status of a device