Last Updated: April 2, 2026
The LoginTC Entra ID EAM integration allows you to use LoginTC as an external authentication method for Entra ID, including for any third-party application that uses Entra ID as an identity provider.
Subscription Requirement
Your organization requires the Business or Enterprise plan to use the Entra ID EAM integration. Explore Pricing Plans
After entering the username and password into the Entra ID protected service, the user is shown a selection of LoginTC authentication methods. The user selects and option, authenticates and logged in.
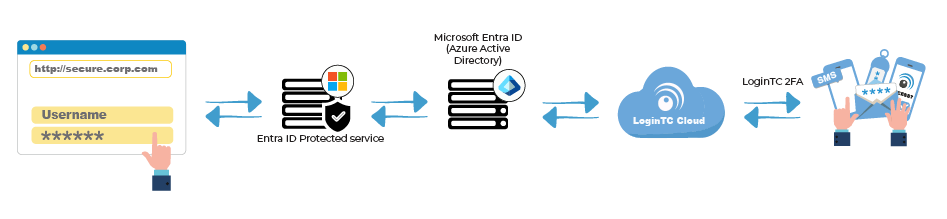
Authentication Flow
- A user attempts to access an Entra ID protected resource from a browser with their username / password
- A Conditional Access policy redirects the user’s browser to LoginTC
- The user is presented with LoginTC authentication methods
- An authentication request is made to LoginTC Cloud Services
- The user response (approval or denial of request) is sent to LoginTC Cloud Services
- The user approval is sent back to Entra ID
- Entra ID validates the response and redirects the user to the protected resource
Before proceeding, please ensure you have the following:
- LoginTC Admin Panel account
- Microsoft Entra ID tenant with P1 or P2 licenses assigned to users
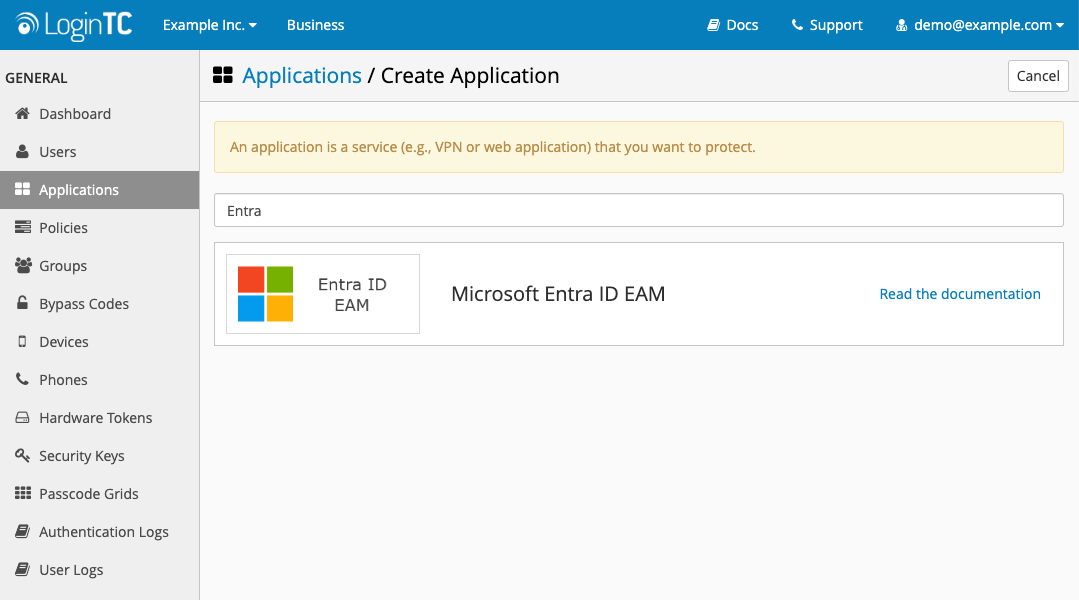
Create a new Application in the LoginTC Admin Panel and connect it to your Entra ID tenant:
- Click on Applications in the side menu
- Type in Entra
- Click on Microsoft Entra ID EAM
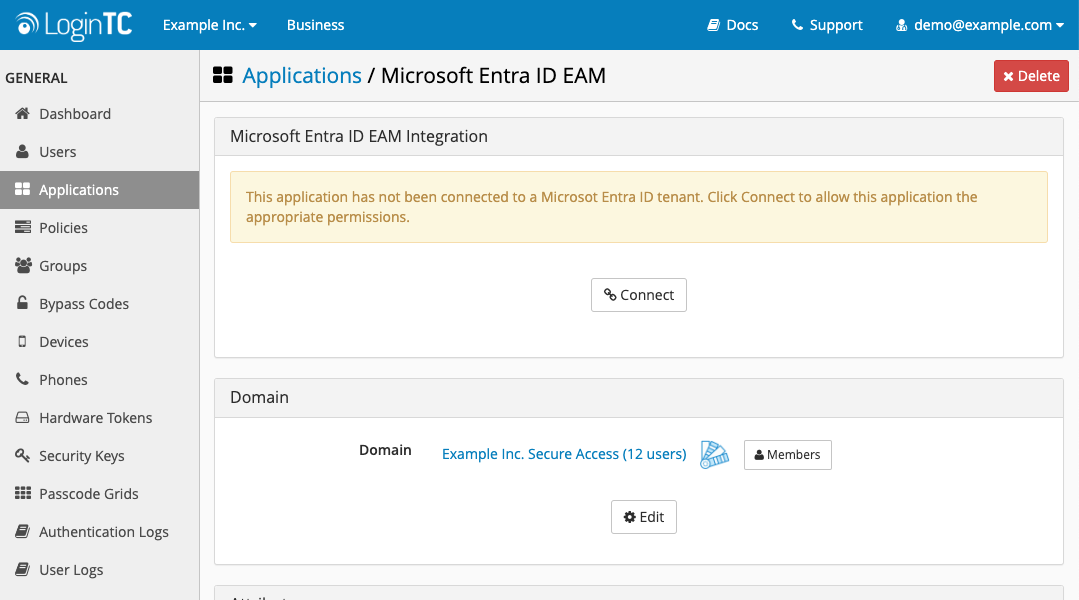
- Scroll down to the Microsoft Entra ID EAM Integration section on the newly-created application
- Click on Connect
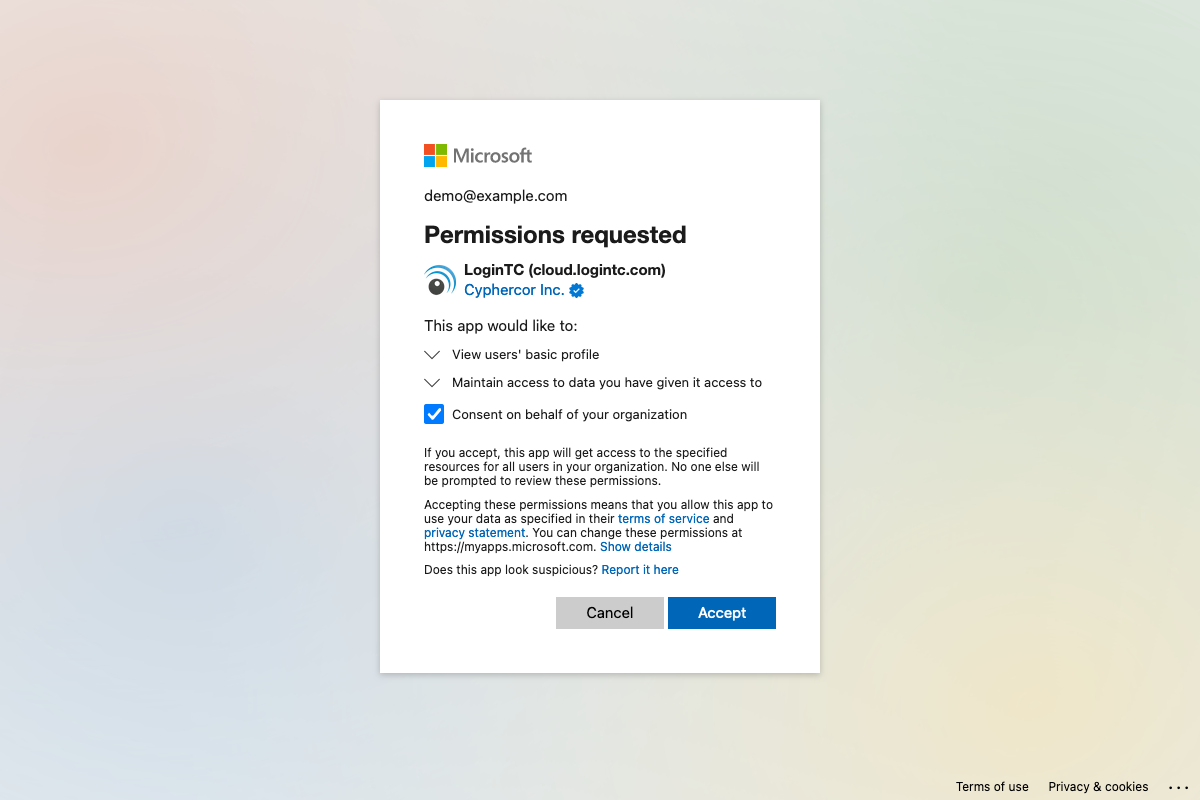
- Sign in to Microsoft with an Entra ID administrator account
- Review the required permissions and select Consent on behalf of your organization
- Press Accept
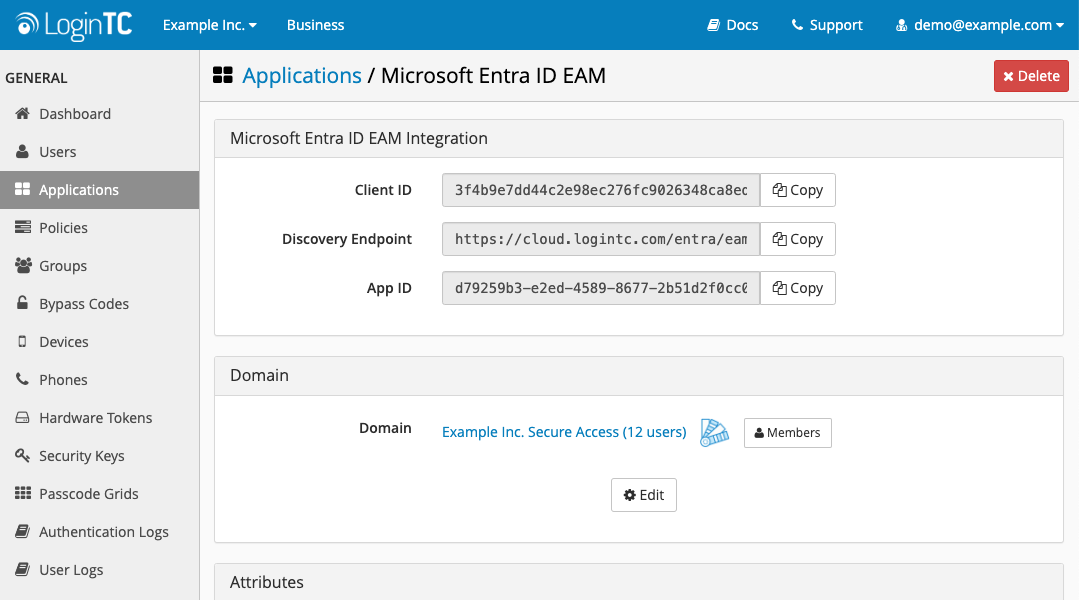
Use the Microsoft Entra ID EAM Integration details displayed on the connected LoginTC application to create an Entra ID External Authentication Method:
- Scroll down to the Microsoft Entra ID EAM Integration details section
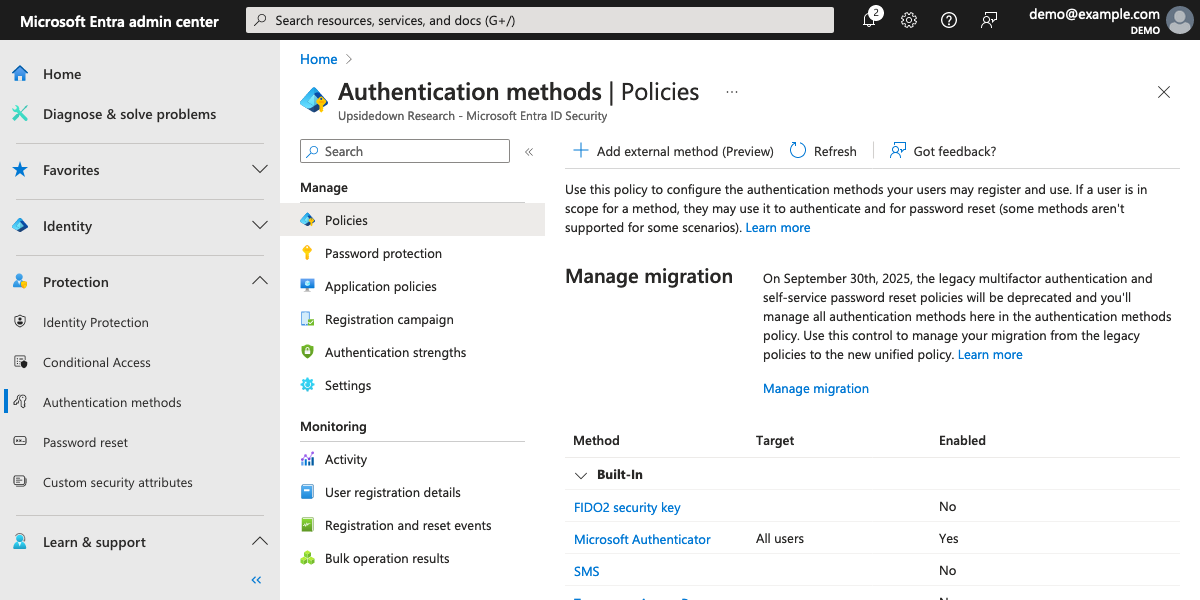
- Open the Microsoft Entra admin center
- Click on Authentication methods under Protection
- Click on the Add external method (Preview) button
- Enter LoginTC for the name
- Copy and paste the Client ID, Discovery Endpoint, and App ID values from the LoginTC application page
- Ensure that Enable is toggled on
- Target all users (or specific users and groups)
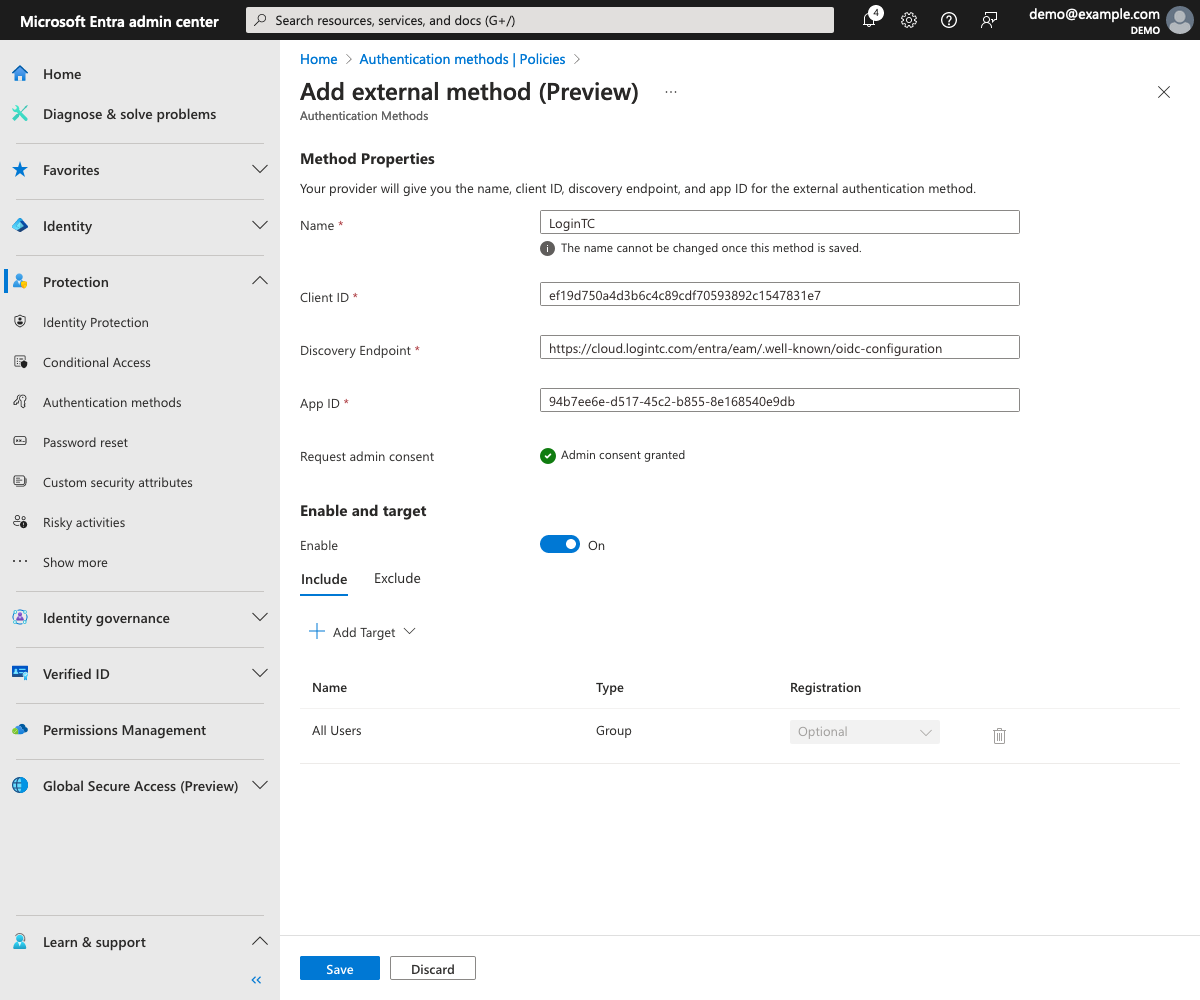
- Press Save
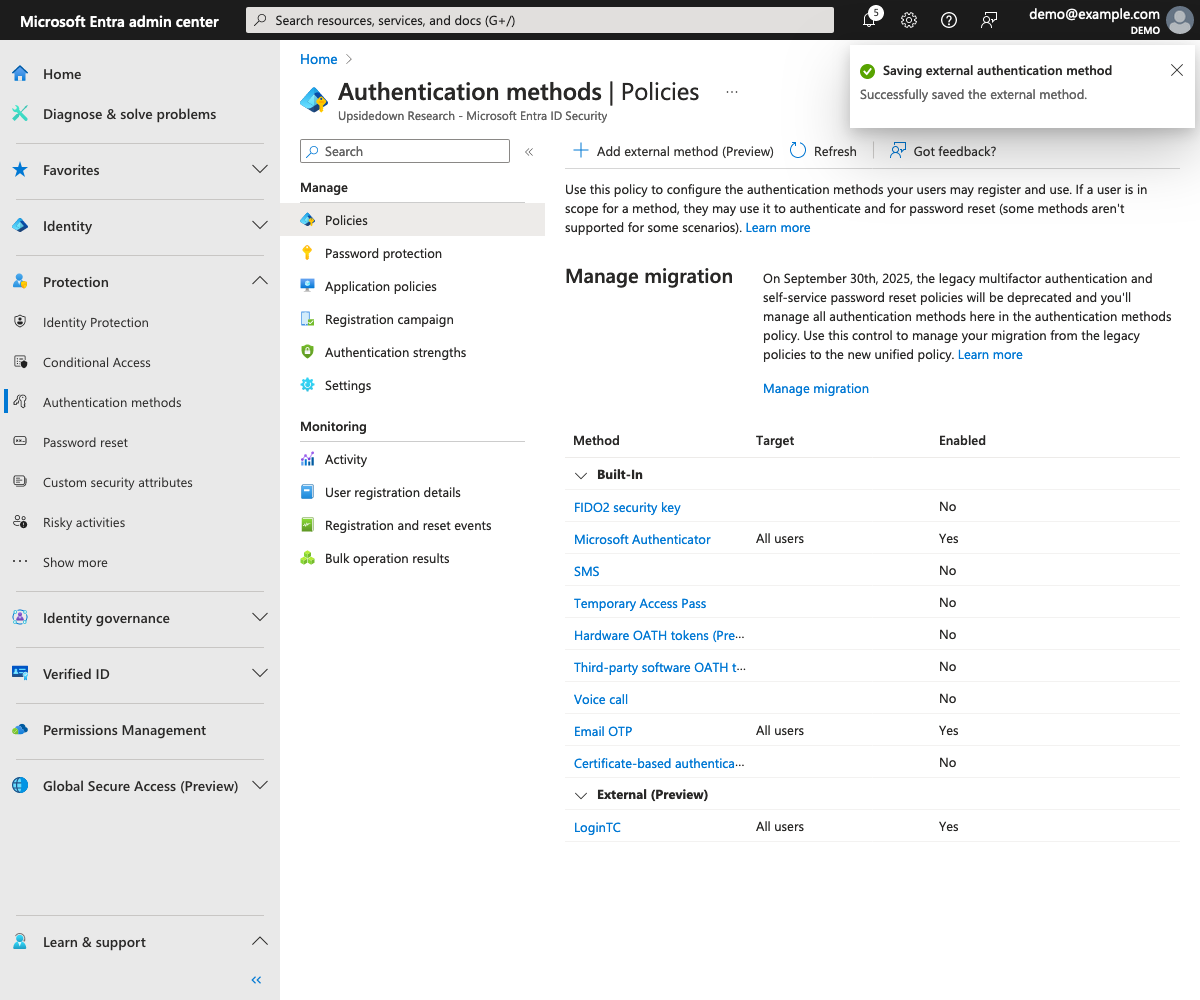
- LoginTC will be added to the list of authentication methods
Create a new conditional access policy in your Entra ID tenant to require MFA for access:
- Click on Conditional Access under Protection
- Click on New policy
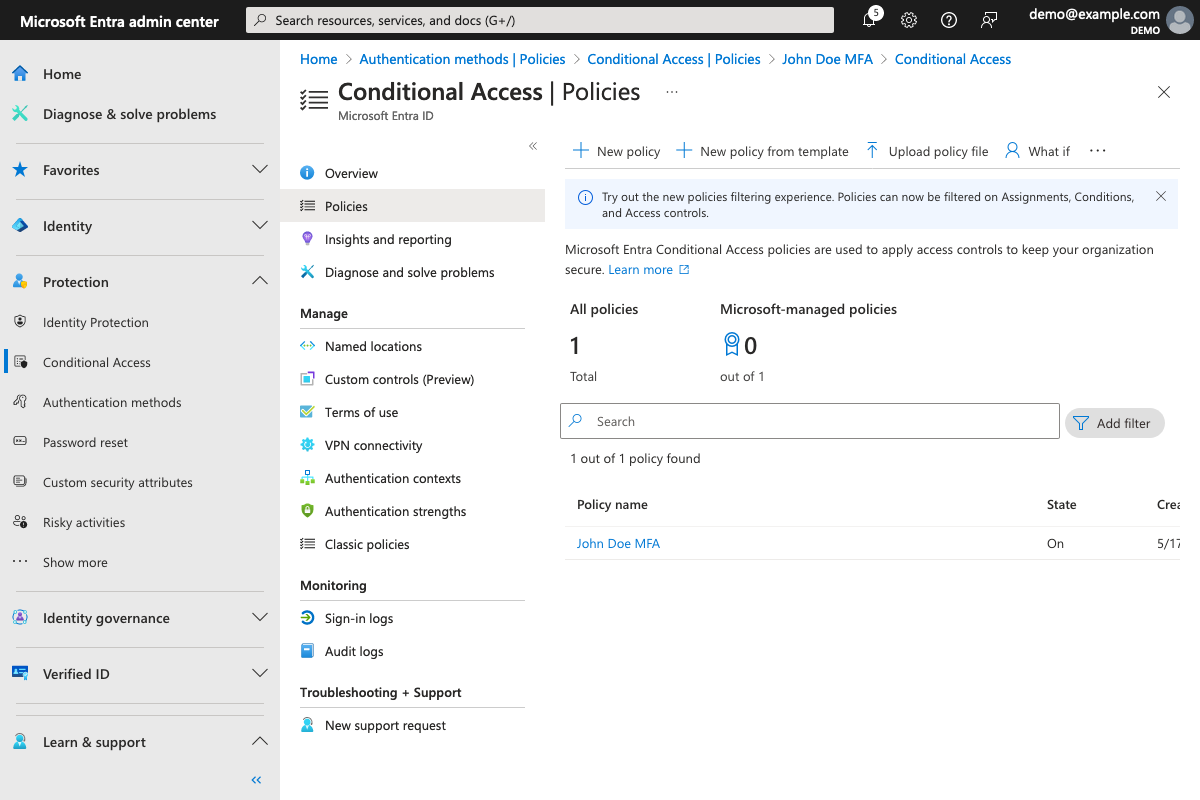
- Give the policy a name
- Select one or more users or groups
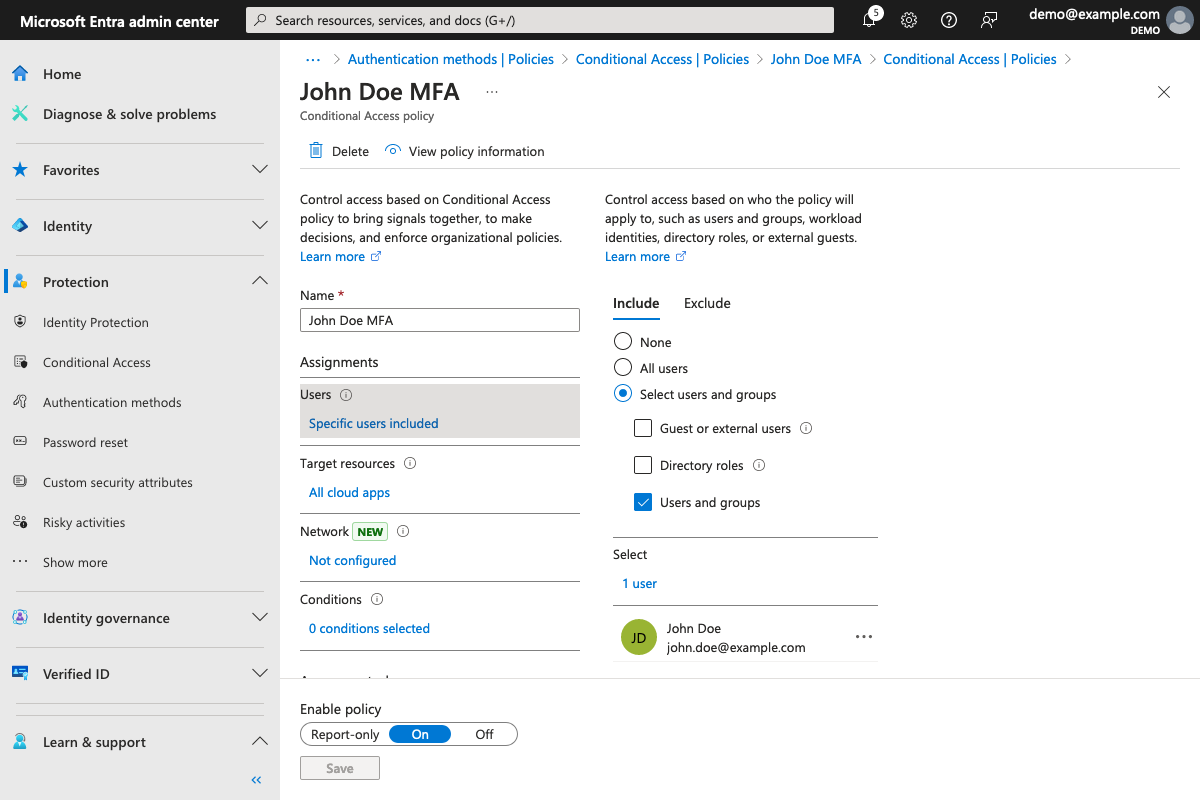
- In the Grant section, select Require multifactor authentication
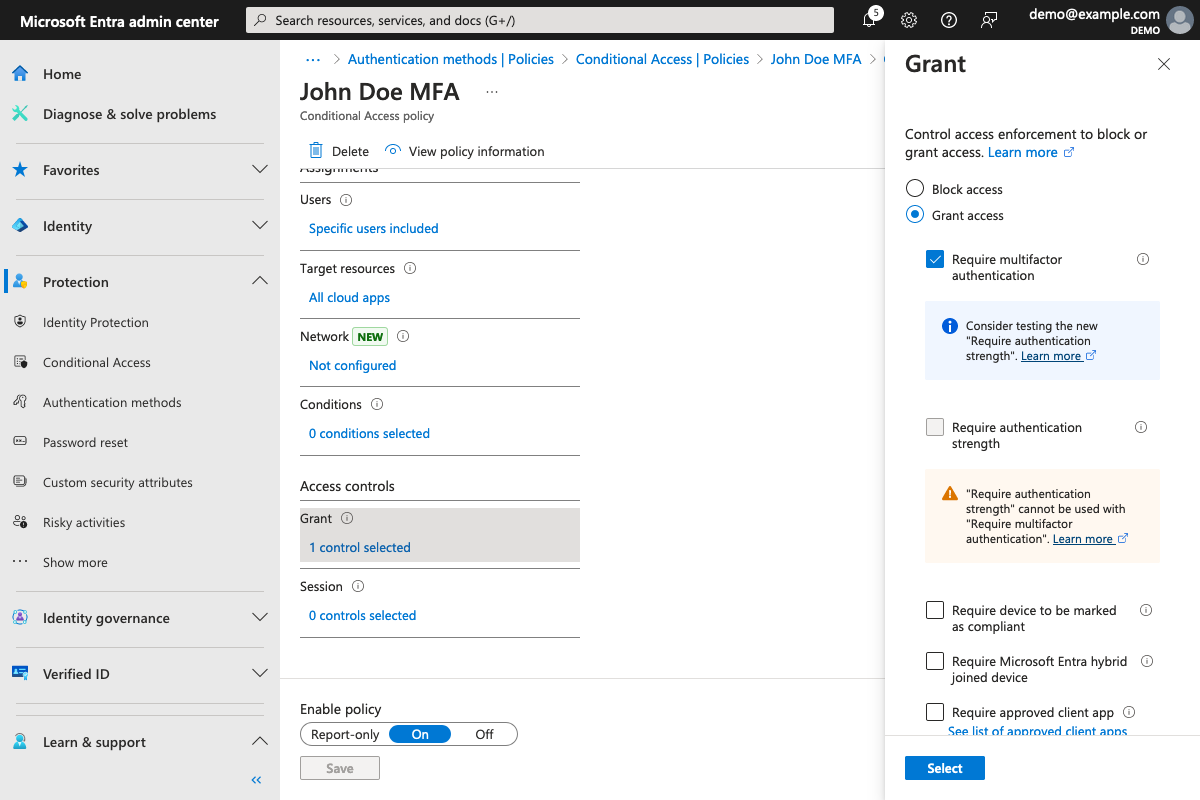
- Save the policy
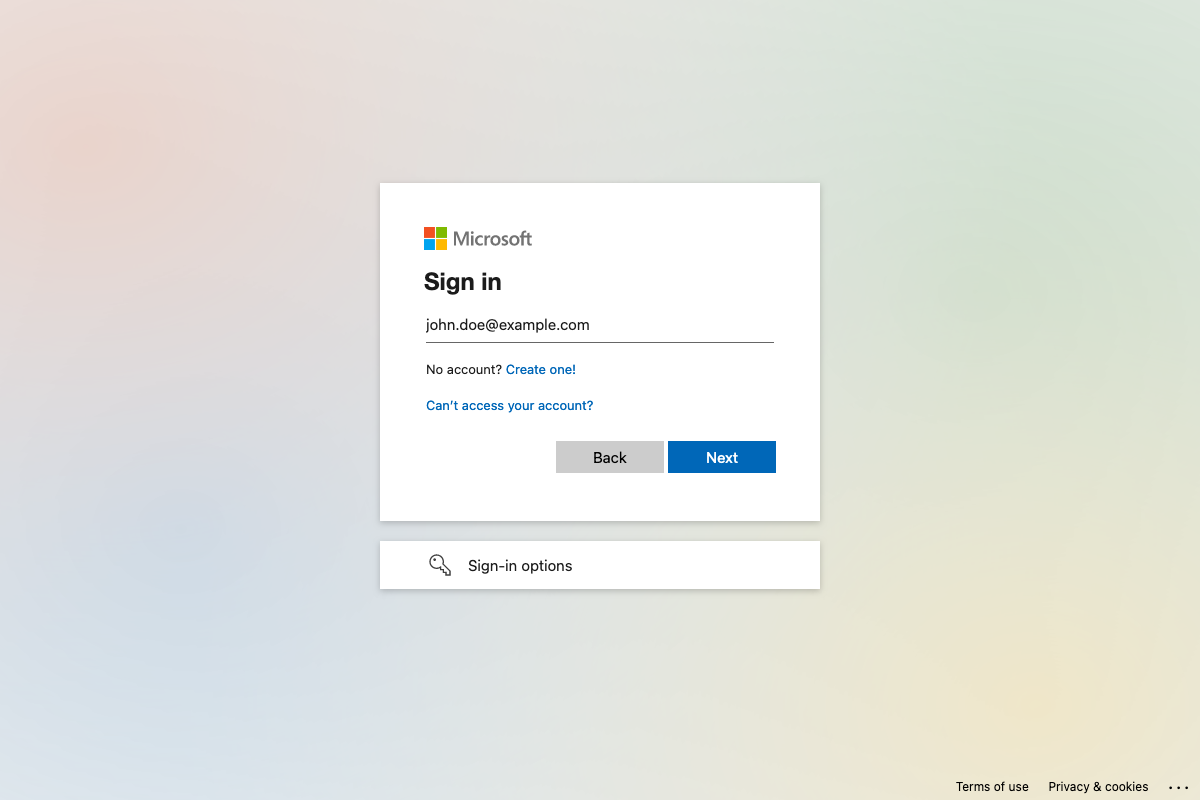
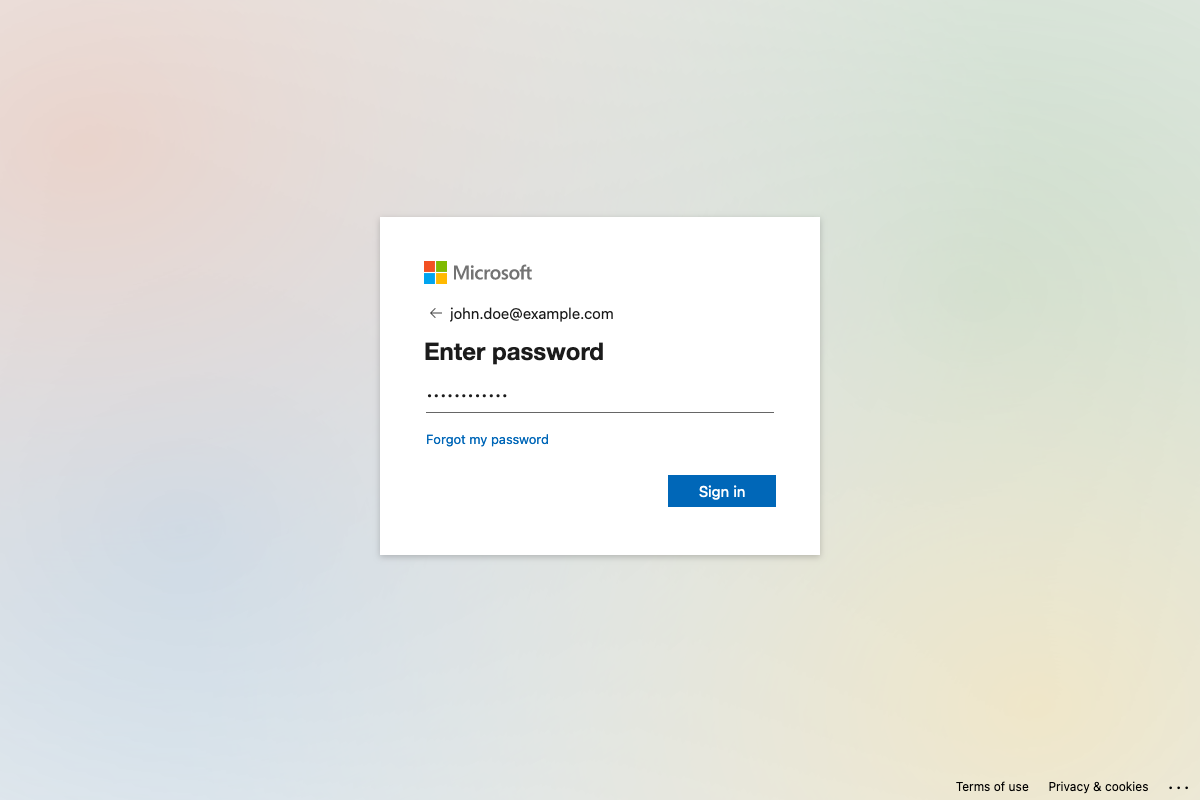
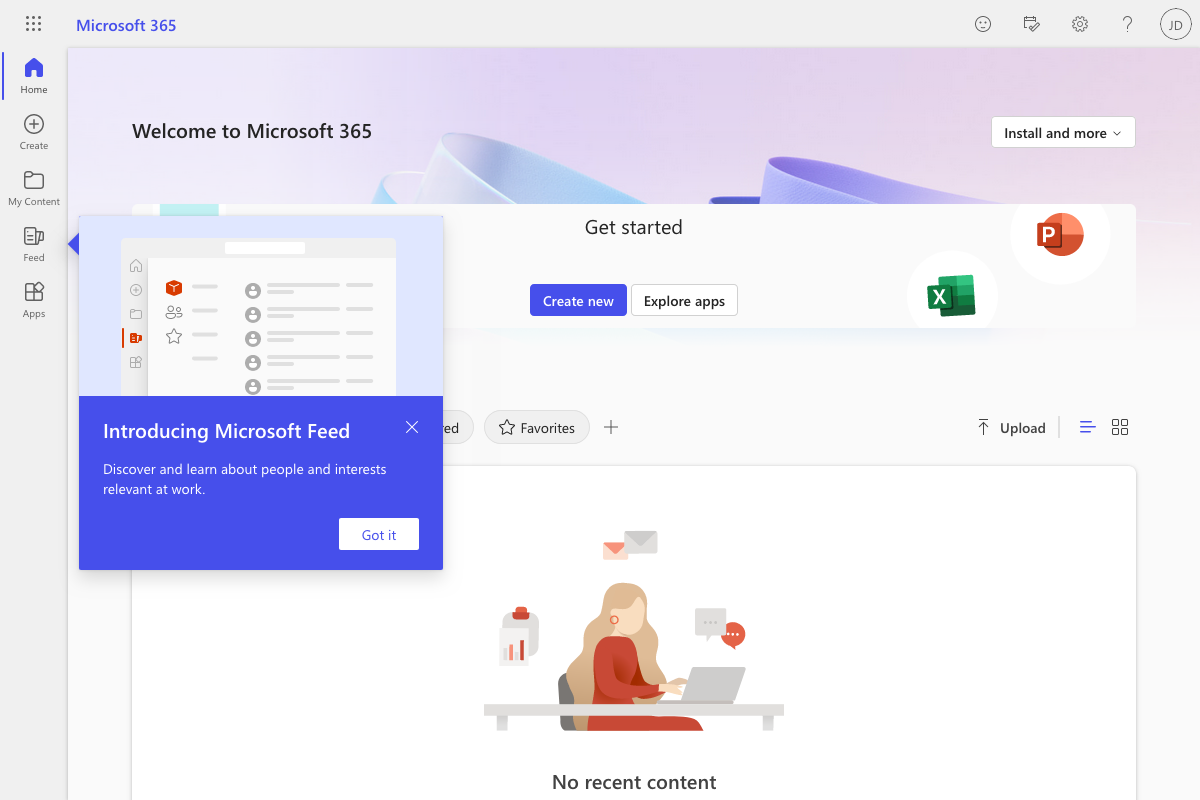
End users will be prompted to log in with LoginTC when they log in to Entra ID or any application that uses Entra ID as its identity provider:
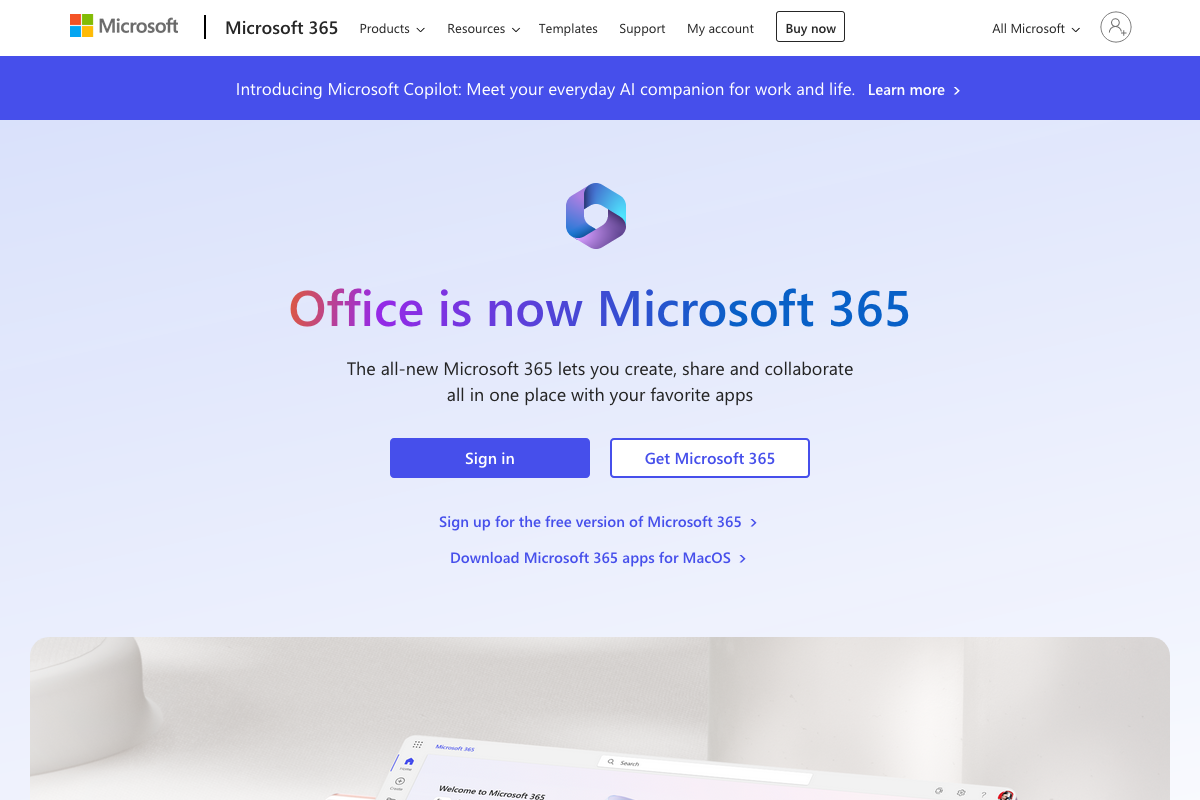
- The user accesses an application (such as office.com)
- The user enters their Entra ID username
- The user enters their Entra ID password
- The user is presented with Entra ID configured multifactor authentication options
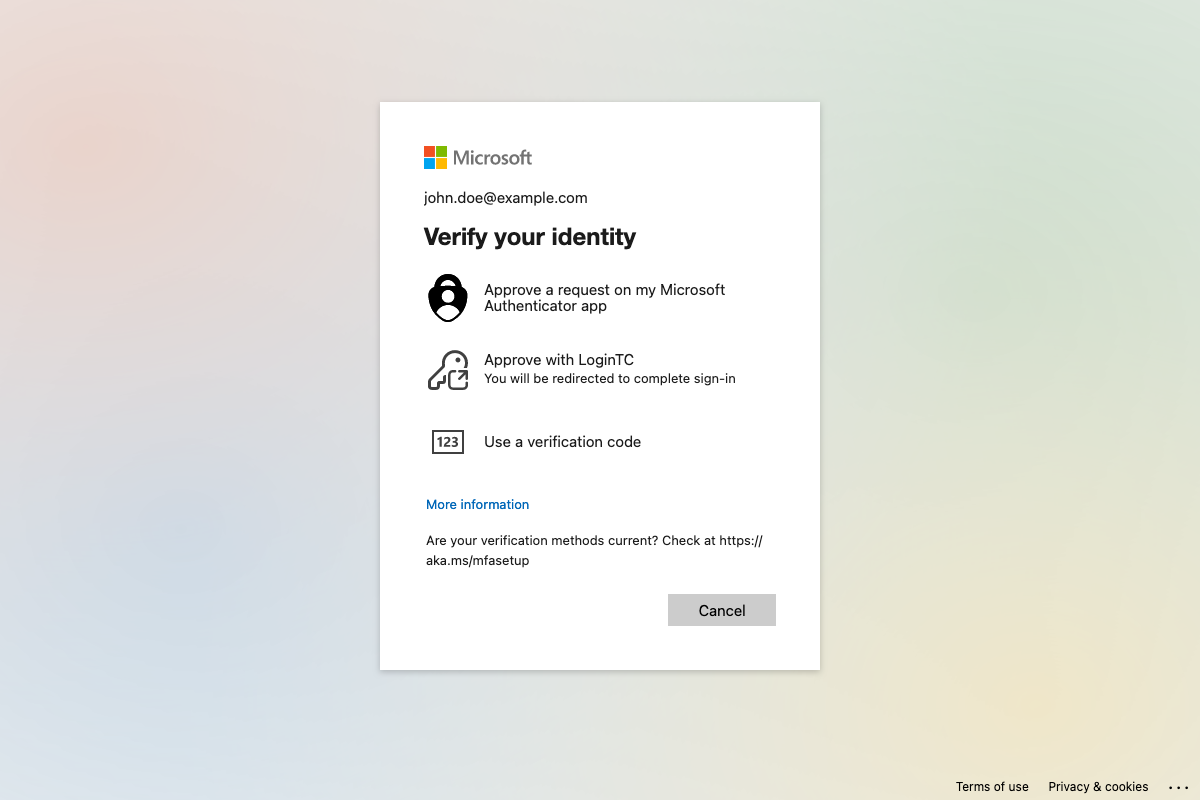
- After clicking on LoginTC, the user is redirected to LoginTC and presented with their LoginTC authentication methods
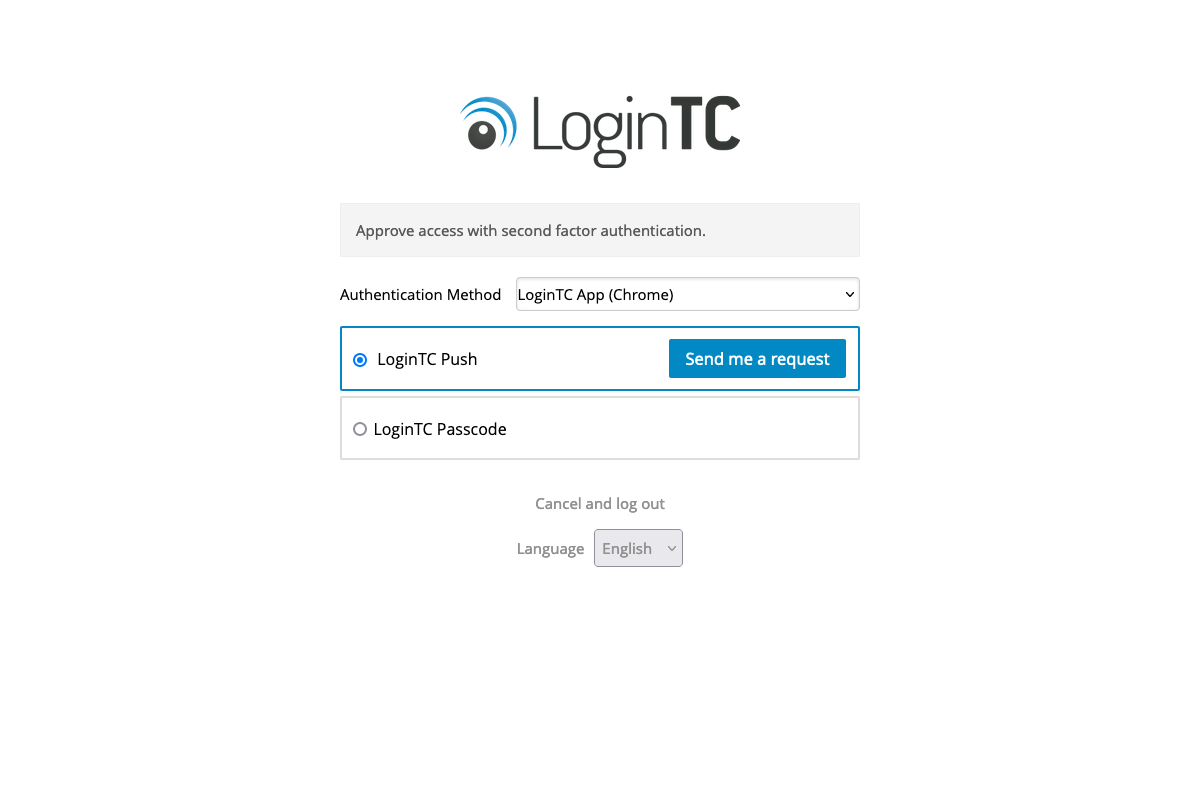
- After successfully authenticating with LoginTC, the user is redirected back to the application
Email Support
For any additional help please email support@cyphercor.com. Expect a speedy reply.