10 simple steps: How to connect your smartphone or tablet to a Cisco VPN using two factor authentication
January 28, 2015 •
Introduction
If you’re like most SMBs, you use a virtual private network (VPN) to access corporate resources and applications, such as important documents, sensitive data and email. And, considering that recent years have seen a rise in remote work and flexible working practices, you probably need to access those assets outside the office, too — whether you’re at home, at a coffee shop, or travelling.
For that reason, mobile devices — light, portable and, these days, ubiquitous — have become the ideal medium for connecting remotely. But maybe you find yourself hesitant to connect to a workforce VPN on your smartphone or tablet. And with good reason. Remote access can be risky, especially if using password-only (single factor) authentication when you log in. So, you decide your access regimen should incorporate two-factor authentication. The problem? Most two-factor authentication systems are cumbersome, pricey, and far from secure.
The solution? LoginTC two-factor authentication eliminates the hassle of carrying around hard tokens or racing against the clock to type in a one-time password (OTP). Not to mention that OTPs via SMS (for example, Google 2-step) can be copied, especially in public venues. Instead, LoginTC turns the very mobile device that’s at hand into a powerful second factor credential. The result? Seamless and safe single-screen connection to a workforce VPN or portal. Getting started is easy. We’ll explain how below.
How to access a Cisco ASA VPN* on smartphone or tablet securely, using two factor authentication (in 10 simple steps!):
*If you don’t have a Cisco ASA VPN appliance, this process still works for any RADIUS-enabled device. Just find instructions for loading a LoginTC connector on your specific device on our Connectors page, and choose a VPN client (whether built-in or third-party app) that works with your appliance.

Note: If you’re an IT administrator, start at step 1. If you’re an end-user, start at step 4.
1. Make sure your VPN is provisioned to allow remote access.
2. Install and configure the LoginTC RADIUS connector VM on your virtual host server in under an hour. The LoginTC RADIUS connector is a free virtual appliance that integrates with RADIUS-enabled devices, such as Cisco ASA. There are step-by-step instructions here.
3. Sign up for a LoginTC admin account. From there, you can add and manage domains and users, as well as issue/revoke tokens. All the instructions are here.
4. Download the free LoginTC app on your smartphone or tablet (iOS, BlackBerry, Android).
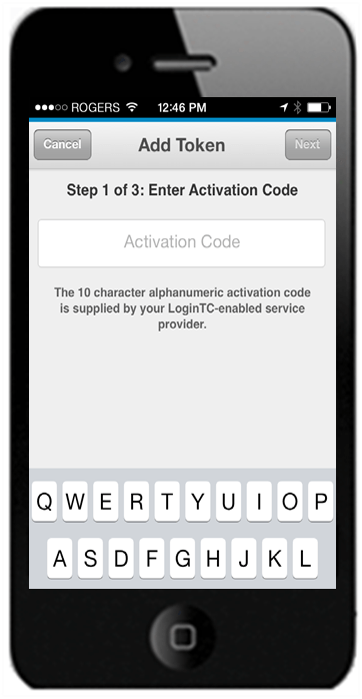
5. Load a credential for your office VPN in your LoginTC app. Just tap the plus sign on the upper right corner of the app and enter the alphanumeric activation code that your administrator should have issued to you. This will pair your device with your VPN account. Then, lock the token by creating a numeric PIN or a passcode (depending on what the administrator has configured).
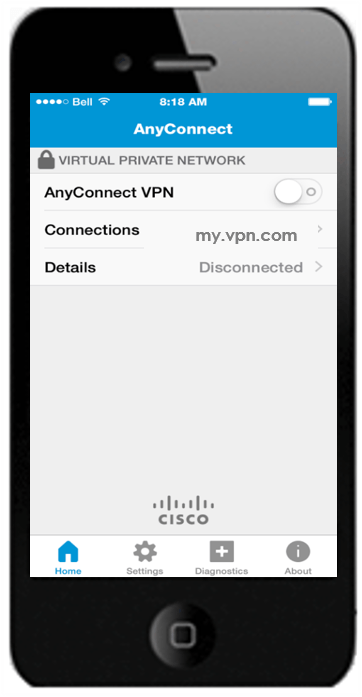
6. Download the Cisco AnyConnect VPN client app on your smartphone or tablet.
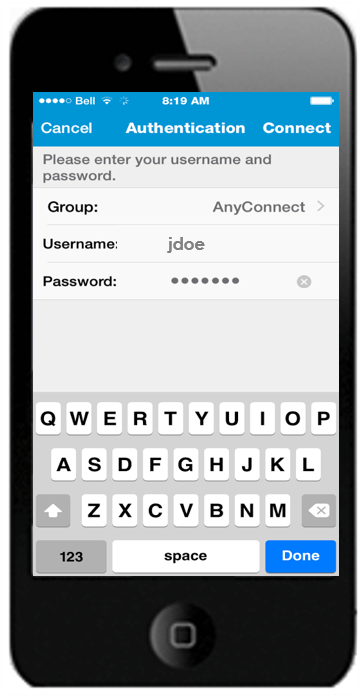
7. Access the VPN. To access the VPN, launch Cisco AnyConnect on your smartphone or tablet and “Add VPN Connection” by inputting your “Server Address.” To log in, enter your first-factor identification (username/password). At this point, unbeknownst to the app, it is in waiting: the LoginTC Connector, which was connected to your VPN earlier, has trapped the first-factor authentication and is orchestrating the two-factor authentication sequence, meaning it will only accept the request to access the VPN through the app once both factors have been satisfied. Once the LoginTC Connector gets a successful confirmation of the username/password, it initiates a wireless notification to your smartphone.
8. Approve the request that has been pushed to your smartphone or tablet. Opening the notification launches the LoginTC app where you can accept the access request.
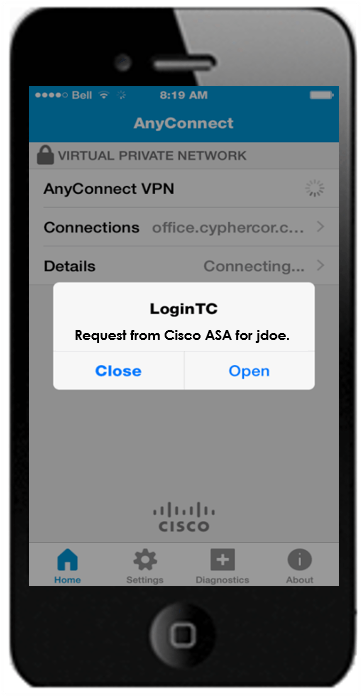
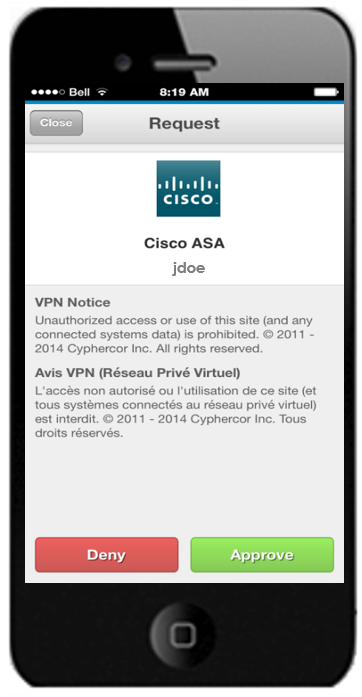
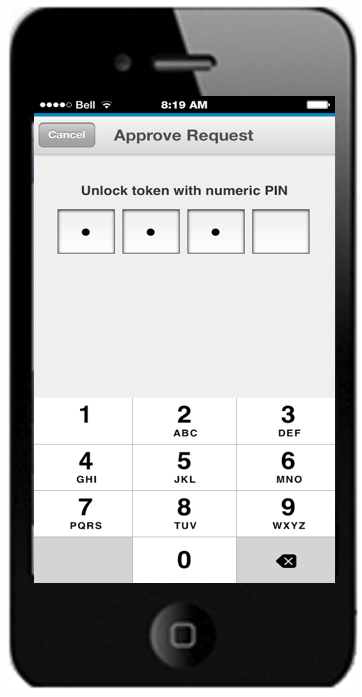
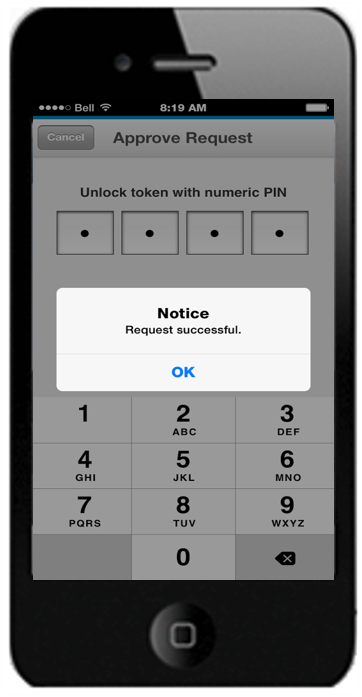
9. Unlock the token with your 4-digit PIN or passcode. Once the correct PIN or passcode is entered, the configured LoginTC RADIUS Connector will confirm the successful unlocking of the VPN token credential and grant you access to the VPN through the VPN client.
10. Connect to your VPN. At this point, if you re-open your VPN client, it will signify that you are connected to the VPN. A VPN symbol should also appear on your device’s status bar.

Now you can use the browser on your smartphone or tablet to safely access internal URLs, enterprise apps etc. that only work behind the VPN! Congrats! We told you it was easy.