The need for contextual information within multifactor authentication
February 19, 2015 •
Putting it into context
It’s no secret that context is an important component of good security. Does your bank call you every time you charge a purchase to your credit card? Of course not. That would be highly inconvenient and, as we know, people are far less likely to embrace new practices (technological or otherwise) if the practices interrupt their lifestyle. Rather, banks use contextual information — Is this an irregular purchase from an irregular location? — to determine whether you should be notified, whether charges are legitimate or fraudulent, and whether you’ll be held responsible for payment.
Coming into play with 2FA
Two-factor authentication (2FA) can and should also leverage contextual information for the purpose of increased security and threat alert / fraud detection. In fact, Gartner, a leading American information technology research and advisory firm, predicted that “by year-end 2016, more than 30% of enterprises will use contextual authentication for workforce remote access — up by about 5% today” (Magic Quadrant for User Authentication, 2013 Report).
As a reminder, two-factor authentication is a cybersecurity solution which requires that two independent factors be present should a user attempt to gain access to an online account. The first is “something you know” (usually, a traditional username/password). The second is “something you have” (a randomized code, one-time password or some form of token).
However, sometimes a third factor comes into play: “something you are.” That three-tier system is called multifactor authentication (MFA), and often refers to biometrics (like iris or fingerprint scans). But what if “something you are” could be determined in other ways — for instance, using contextual information, the way credit card companies have been. Well, human traits and behaviour (such as your location behaviour) are “something you are” and therefore can act as a third factor.
Best practices
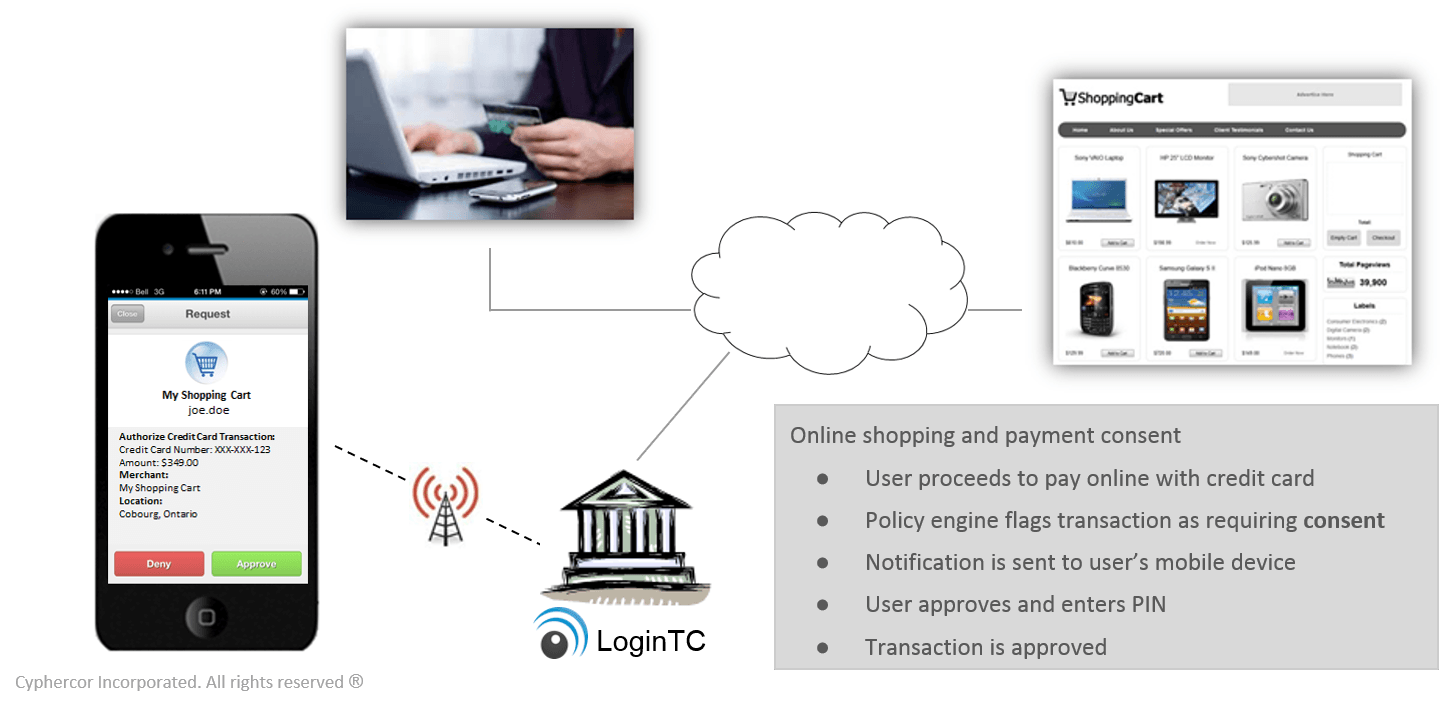
There are various ways contextual information could be incorporated into the 2FA / MFA landscape. Some leading 2FA providers, particularly those that deploy 2FA via one-time passwords on hard tokens, have come out suggesting that financial institutions implement the “step-up” (also known as “progressive authentication” or “trust elevation”) method. This means to say that when high-risk activity occurs — either as detected by their existing context-based systems or by a pre-determined dollar amount, such as transactions over $100,000 — only then is second factor authentication enabled. The argument is that authentication should match risk to balance security with user experience.
Gartner agrees that interest and support for contextual information is driven by “finding an appropriate balance between authentication strength, total cost of ownership (TCO) and user experience (UX).”
However, we at Cyphercor believe there is a better option — one that also meets all of the above criteria. LoginTC 2FA can provide every user with contextual information every single time without a shred of inconvenience (not to mention its high security and low cost).
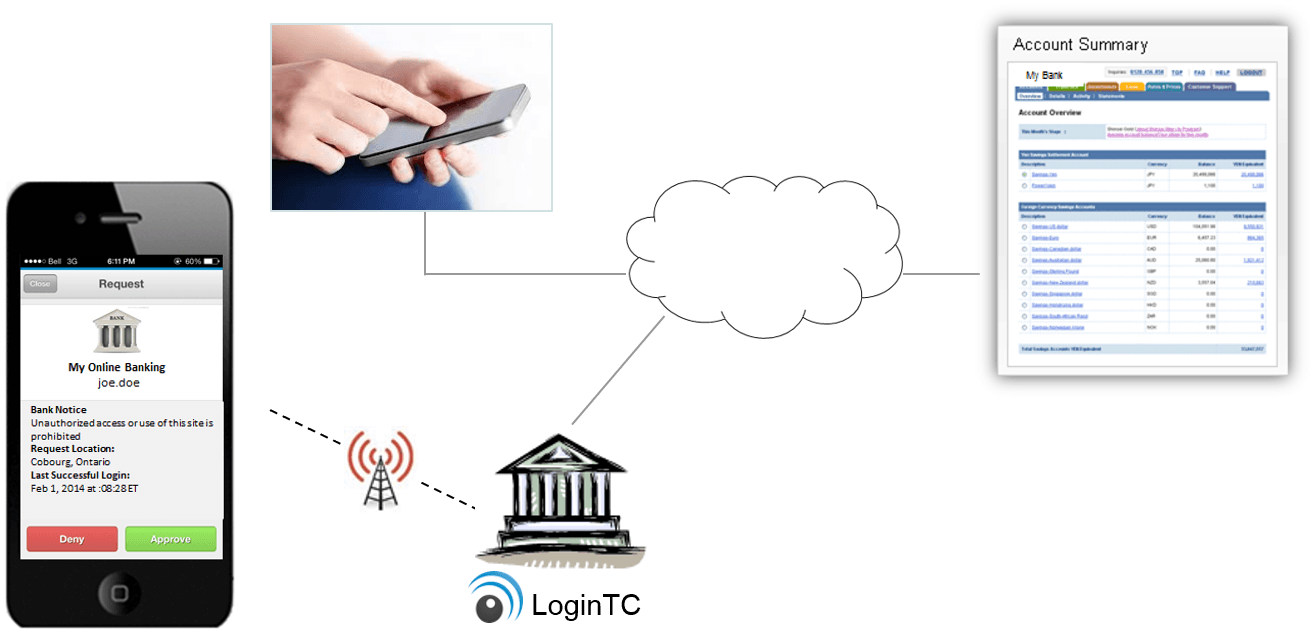
Introducing LoginTC
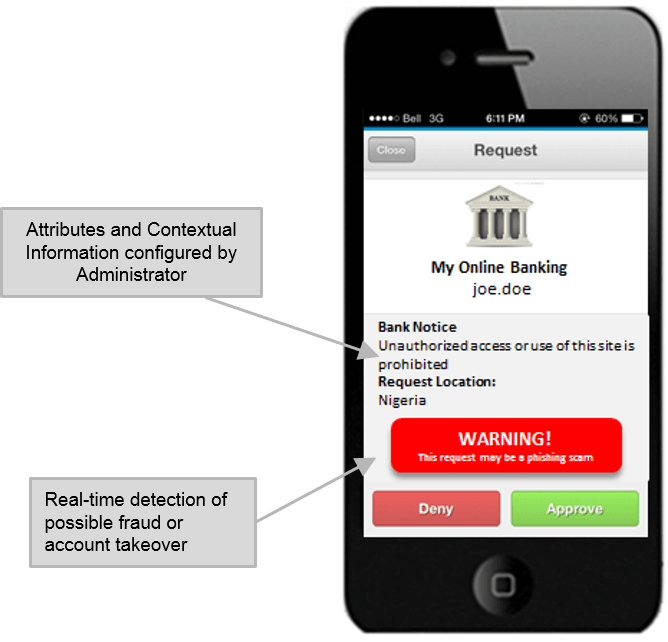
LoginTC weaves real-time contextual information (e.g. geolocation) into its already easy-to-use design by integrating it into notifications that get pushed to end-users’ mobile devices (smartphone, tablet) or desktops (via Google Chrome) where they accept or deny access requests with a simple tap. The beauty of LoginTC also lies in the symbiosis between push notifications that work worldwide and the pressing need for identity management in remote and foreign places. In other words, a remote attacker should not be able to hack your account, but you should also be able to access your account without a hitch while you are working remotely — whether at a coffee shop or in Timbuktu.
Conclusion
Phone-as-token, the LoginTC method of deployment (although we also support tablets and desktops), is the best way to seamlessly integrate context into 2FA. How can you add contextual information to a hard token? Where would it fit in beside an OTP? And how would adding contextual information to a text message help if the SMS has been intercepted?
After all, according to Gartner, “adoption of contextual authentication in the context of adaptive access control will provide further impetus for the migration from legacy OTP hardware tokens toward ‘tokenless’ solutions.”
The Gartner report looks toward the future, forecasting things like “contextual authentication will happen in a certain way by a certain year.” But LoginTC is optimizing contextual information right now in a way that legacy 2FA providers cannot do due to limitations in their infrastructure. Why wait to be fully secure? Why not get on-board immediately and gain a leg up on your competition?
LoginTC: The future of authentication. Right now. Get started in minutes with a free trial.