MFA for Windows Logon and RDP
Secure every Windows login with LoginTC multi-factor authentication (MFA). Whether users are logging into a local workstation, connecting over Remote Desktop Protocol (RDP), or working entirely offline, LoginTC adds a reliable second factor to every authentication event without replacing your existing Active Directory infrastructure.
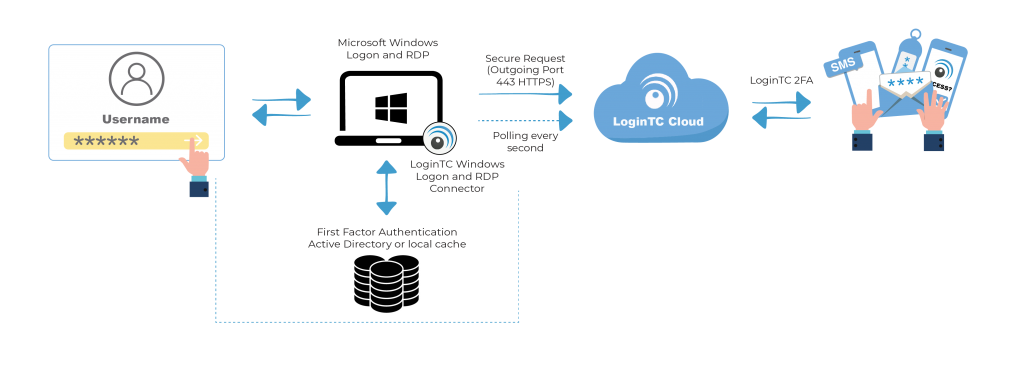
Fast to deploy, simple to manage, and built for on-premises environments. Explore how LoginTC can work for your organization.











 AD Integration
AD Integration  MFA Cannot Be Bypassed
MFA Cannot Be Bypassed